 Looking to make a little quick cash? You could buy lottery tickets, but you have a better chance of being struck by lightning than winning the big one. Keep telling yourself that someone has to win. In modern society, the quick payout isn’t necessarily a real thing. Sure, it happens, but it usually requires a ton of luck or a willingness to do something illegal. No, in today’s society, knowledge is worth something, and it can be exchanged for money if you have the correct knowledge. Case in point: if you have some specific information, the Federal Bureau of Investigation is willing to pay for it.
Looking to make a little quick cash? You could buy lottery tickets, but you have a better chance of being struck by lightning than winning the big one. Keep telling yourself that someone has to win. In modern society, the quick payout isn’t necessarily a real thing. Sure, it happens, but it usually requires a ton of luck or a willingness to do something illegal. No, in today’s society, knowledge is worth something, and it can be exchanged for money if you have the correct knowledge. Case in point: if you have some specific information, the Federal Bureau of Investigation is willing to pay for it.
You may be familiarwith the GameOver Zeus botnet. It’s been aware of us for a while – as early as 2011. According to CNET, “GameOver Zeus, which first emerged in 2011, is an offshoot of the original data-stealing Zeus Trojan that began appearing in 2007, the [United States] Justice department said. However, its peer-to-peer structure differs from earlier variants of Zeus, which infected more than 13 million computers worldwide and led to losses of hundreds of millions of dollars.” Before it was taken down in June, 2014 in a joint operation by the FBI, Europol, and the National Crime Agency of the UK (dubbed ‘Operation Tovar’), GameOver Zeus infected somewhere between 500,000 and one million computers, and successfully stole well in excess of US $100 million from unsuspecting victims.
The botnet was used to steal banking credentials and “was disrupted by a multinational law enforcement investigation that seized servers central to the administration of highly sophisticated malware called Cryptolocker, which encrypted victims’ computer files and was then used to demand a ransom of hundreds of dollars in exchange for the encryption key to unlock the files.” In addition to targeted attacks, the GameOver Zeus campaign used traditional phishing methods to target its victims. “Often downloaded onto unprotected computers from malicious websites created by cybercriminals, the malware can also be spread via phishing scams that entice users to click on a link or attachment that installs the malware on victims’ computers. A keylogger then records victims’ account numbers and log-ins, which are then transmitted to the botnet’s servers.”
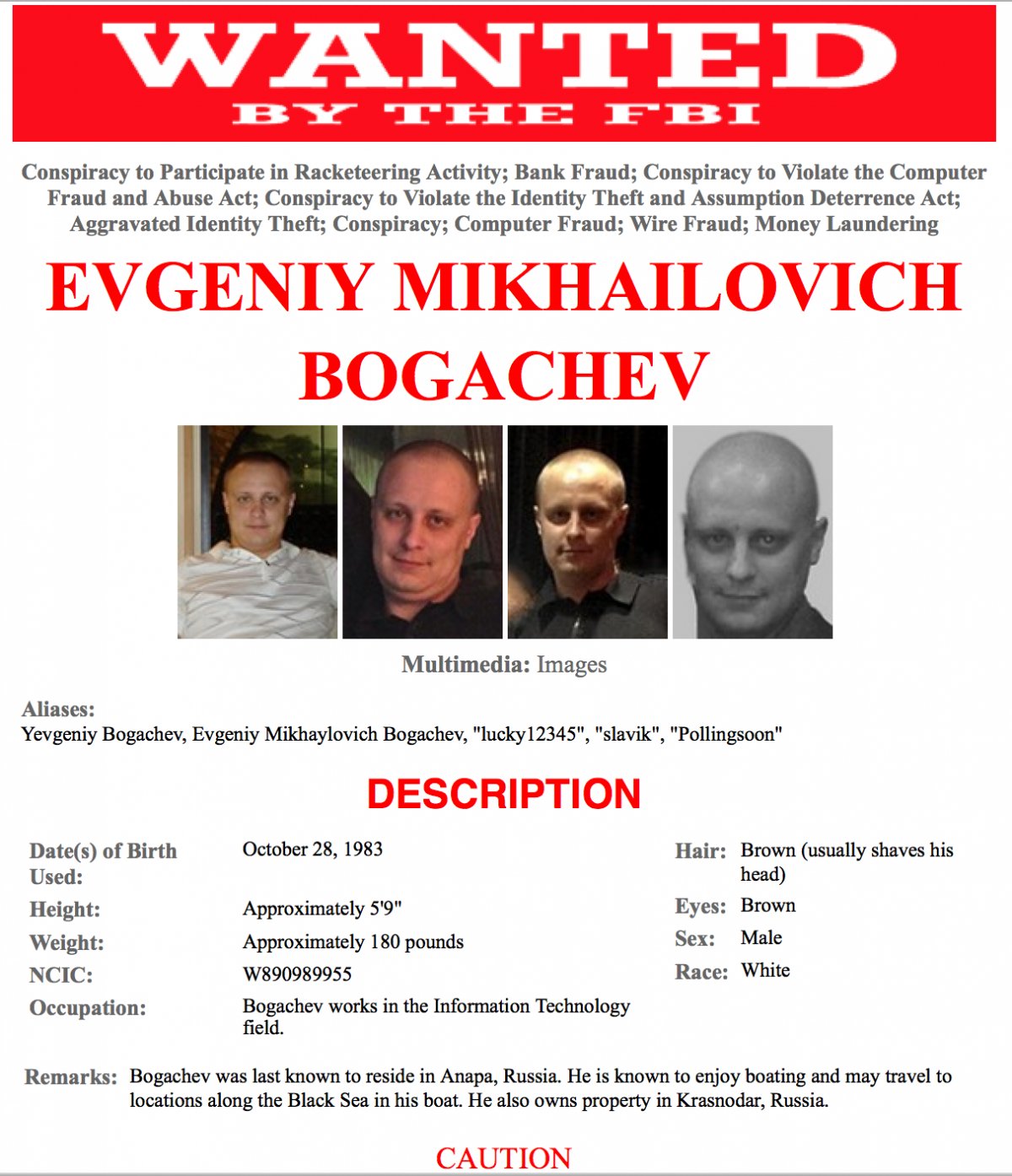
In the June indictment that accompanied the botnet’s takedown, the US Justice Department charged Evgeniy Mikhailovich Bogachev, a Russian nationalist in absentia, with 14 counts, including conspiracy, computer hacking, wire fraud, bank fraud, and money laundering. Believed to be living in Anapa, Russia, Mr. Bogachev probably didn’t worry too much about the indictments, because there’s no formal extradition treaty between the United States and Russia.
He might want to start worrying now, however, because the US government has just upped the ante. Last week, CNET reported that the FBI has offered a US $3 million reward for Mr. Bogachev, and that number is a record figure. The FBI’s website list, among others, Mr. Bogachev’s crimes as including Conspiracy to Participate in Racketeering, Aggravated Identity Theft, and Conspiracy to Violate the Computer Fraud and Abuse Act.
In a statement by the US Department of Justice, the US government states that Bogachev, “Also known online as “lucky12345” and “slavik,”…allegedly acted as an administrator in a scheme that installed malicious software on more than one million computers without authorization. “ Bogachev, the statement says, “is believed to be at large in Russia. This reward offer reaffirms the commitment of the U.S. government to bring those who participate in organized crime to justice, whether they hide online or overseas.” In addition to the charges levied against Bogachev, he remains on the FBI’s Cyber’s Most Wanted list, a who’s who of the people that give us fits and disrupt our sleep patterns.
Known as the U.S. Department of State’s Transnational Organized Crime (TOC) Rewards Program, the funding of rewards was established in 2013 by US Congress “to assist efforts to disrupt and dismantle transnational organized crime.” The record bounty comes at a time of “increased efforts by the US government to stem the rise in cyberattacks, which the NSA estimates results in the loss each year of between $100 billion and $400 billion worth of intellectual property, according to Threat Post,” writes CNET.
This is great news to those of us who rely on cyber security in our day-to-day lives. Russia, and other parts of the world have in many ways been untouchable, making them safe havens for criminals who wished to carry out their crimes with impunity. While it may not bear fruit for Bogachev, this reward symbolizes a tangible way of getting these crooks off the streets and safely behind bars.
