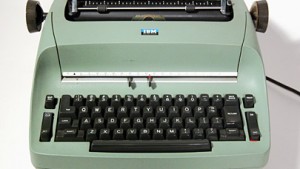
With the world about to end on Tuesday, you probably have more pressing matters on your agenda, like kissing your kids goodbye, donning your tinfoil hat, booking the first available space ark to Mars, and spending some last loving moments with the one you love the most – the Internet – using that quality time to finish those Torrent downloads, grab some Web porn for the long trip, and search for a good recipe for soylent green. But just in case the Earth doesn’t get into a smackdown with an asteroid the size of an aircraft carrier and we’re not all converted into the cosmic equivalent of a badly shipped box of corn flakes, you may want to take note of the latest SSL Certificate security breach. And when you hear how long the purported malware has been infecting their servers, you may be tempted to dust off your old typewriter and dig your fax machine out of the rummage pile in the basement.
With the world about to end on Tuesday, you probably have more pressing matters on your agenda, like kissing your kids goodbye, donning your tinfoil hat, booking the first available space ark to Mars, and spending some last loving moments with the one you love the most – the Internet – using that quality time to finish those Torrent downloads, grab some Web porn for the long trip, and search for a good recipe for soylent green. But just in case the Earth doesn’t get into a smackdown with an asteroid the size of an aircraft carrier and we’re not all converted into the cosmic equivalent of a badly shipped box of corn flakes, you may want to take note of the latest SSL Certificate security breach. And when you hear how long the purported malware has been infecting their servers, you may be tempted to dust off your old typewriter and dig your fax machine out of the rummage pile in the basement.
The encryption method that provides nearly every secure online transaction today is reliant upon third parties – the Certificate Authorities – to ensure that every connection is digitally signed as a reliable source; so what if those certificates are compromised? Well, for starters, we may be taking on some new computer overhead in the form of botnets or spyware. But that’s just speculation, right? CAs offer secure digital transactions and we can all sleep at night, right?
[Sigh]. The hits just keep on coming in a year that has seen massive security breaches and data breaches, the unprecedented rise of hacktivism, the hacking of SSL/TLS, deadly new botnets and smarter spammers. Amidst all these high-profile stories, it may be tempting to turn a blind eye from a number of security breaches at SSL Certificate Authorities in 2011, and in case you were wondering, there have been a few. In fact, more than a half dozen CAs have been breached this year, including four different Comodo resellers, DigiNotar, StartSSL, and the ubiquitous GlobalSign. Now, the fine people over at The Register are reporting that KPN Corporate Market, based in the Netherlands, has ceased issuing any new Secure Sockets Layer certificates after it discovered attack tools stored on its servers.
The tools in question were Distributed Denial of Service (DDoS) attack mechanisms and while that may seem like serious business to most of us, KPN wants to assure us that it probably isn’t anything to worry about. “There is no evidence,” The Register states, “that the compromise affects KPN servers used to generate the certificates that Google, eBay, and millions of other services use to cryptographically prove their websites are authentic, rather than easily created imposters. But the possibility “can not be completely excluded,” KPN officials said in a statement issued Friday (Google translation here).”
Okay, it most likely isn’t anything. Well, it could be something, but how can anyone possibly know? I mean, it’s not like the malicious software has been sitting there on the certificate servers, for like, oh, I don’t know, four years or anything. Right?
KPN states that they were taking action while they continue to investigate the breach, “which may have taken place as long as four years ago.”
C’MON, MAN! Four years? Are you freaking kidding me? To put that into perspective, that’s one-fifth of the lifetime of the World Wide Web. CA’s are supposed to be the front line of defense against botnets, spyware, adware, and a host of other security risks. I don’t know if it’s even possible (I’m sure it is) to estimate just how many certificates have been assigned in four years, but when you consider the aforementioned breaches of other CAs – all this year – it makes one wonder if we’ve been treading water in the River Styx all these years. “The compromise underscores the fragility of an SSL system that’s only as trustworthy as its most insecure, or most corrupt, member,” notes The Register. Around since 1994, there is plenty of speculation today to suggest that SSL is truly broken.
The Register points out that there are more than 600 CAs trusted by today’s mainstream browsers and all that’s needed to forge a replica of a credential for [insert website here] is unauthorized access to one CA. From an anti-spam perspective, it’s bad enough that we have to worry about the websites that represent a clear and present danger. What happens when we can’t trust any sites?
Why don’t you type me up a letter on your shiny new IBM Selectric and let me know?