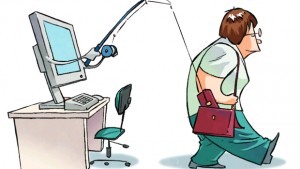
Two words you never want to hear together are ‘massive’ and ‘phishing.’ They’re normally followed by ‘attack,’ and then you could be in for a world of hurt, especially for users who aren’t predisposed to vigilance. So when several media outlets reported this week that US mega bank JP Morgan Chase was hit with a massive phishing campaign, we thought it was worth a look.
Two words you never want to hear together are ‘massive’ and ‘phishing.’ They’re normally followed by ‘attack,’ and then you could be in for a world of hurt, especially for users who aren’t predisposed to vigilance. So when several media outlets reported this week that US mega bank JP Morgan Chase was hit with a massive phishing campaign, we thought it was worth a look.
According to SC Magazine, customers of JP Morgan Chase, the largest US bank by assets, were targeted in a “multifaceted phishing campaign impacting mostly people in the U.S., according to security firm Proofpoint.” And the attackers responsible for the would-be cash grab didn’t try to hide their intent. “The campaign is noteworthy because of how “unsubtle” it is, Kevin Epstein, VP of advanced security and governance with Proofpoint, told SCMagazine.com on Friday, explaining that roughly 500,000 phishing emails have been sent out so far, with about 150,000 going out in the first wave.”
The phishing email messages look very legitimate, according to SC Magazine. They ask “recipients to click to read a secure and encrypted message from JPMorgan Chase.” Crafting visually-convincing messages is critical to successful phishing attacks. The more convincing the message, the more serious the threat, because not only do these messages catch users in the net of deception, but also because they normally suggest the attacker is technically proficient, and more than likely, smart enough to pull it off.
Clicking the link in the message directs users to the phishing page, where their JP Morgan Chase banking credentials are required to continue. And here’s where it gets medieval. The phishing page also contains the RIG Exploit Kit, “which aims to take advantage of numerous vulnerabilities to download a variant of Dyre malware that was initially undetected by anti-virus.”
Among those vulnerabilities, Epstein says, are “CVE-2012-0507 and CVE-2013-2465 for Java, CVE-2013-2551 for Internet Explorer 7, 8 and 9, CVE-2013-0322 for Internet Explorer 10, CVE-2013-0634 for Flash, and CVE-2013-0074 for Silverlight. The RIG Exploit Kit is mounted in a Russian registry; that doesn’t conclusively prove a Russian base, but is suggestive,” Epstein said, adding that the exploit kit is hosted out of Moscow.
If the user enters his or her credentials, they’re redirected to an ‘error’ page, informing them that they need to download and run a Java update called “Java_update.exe.” This is actually Dyre, and installing the malware will have disastrous consequences. Proofpoint’s post outlining the threat can be found here.
Dyre is relatively new. It was discovered in June by researchers with PhishMe. The malware uses a technique known as ‘browser hooking,’ where user credentials are stolen just prior to the information’s encryption. In addition to its payload, Dyre also monitors network traffic and bypasses SSL mechanisms in browsers. It also modifies network traffic and redirects users back to legitimate websites. What makes it even more dangerous is that this appears to be a new strain of the malware, according to Proofpoint. “According to VirusTotal, the version of Dyre used in this attack was not detected by any of the leading antivirus providers at the time of the attack.”
The campaign’s been dubbed “Smash and Grab,” and what makes it extremely dangerous is its multifaceted approach to targeting victims. Epstein told SC Magazine that the campaign “flies in the face of conventional phishing tactics, which involve focused single exploits concealed behind multiple layers of indirection to avoid detection. This is [more of] a physical smash and grab; the attackers relied on speed of delivery and impact.”
What’s notable about this attack is the sophistication and multilevel nature of the campaign. Proofpoint notes three distinct themes. “Since phishing campaigns are quite common it wasn’t until we dug a bit deeper that we noticed some interesting things about this particular attack.
- The credential phishing page is also delivering an exploit kit (RIG)
- Submitting credentials results in a fake Java update that’s really banking malware
- The attacker is using the same infrastructure for PDF and zip based attacks in other active campaigns
“Both of these exploits are attempting to install the recently discovered Dyre banking Trojan that attempts to steal banking credentials,” Proofpoint says.
The sophistication of the attack is very suggestive of a well-organized and well-funded attacker, and it’s no surprise that the trace fingerprints are Russian in origin. Criminal organizations are usually the prime suspect in cases like this, and while there’s no certainty to the Russian ties or organized crime, the inference isn’t difficult to make.